With the evolution of container technology, the manner in which IT operations are performed has considerably changed. Containers offer an ideal solution for how consistently a software can run when it’s migrated from a particular computing environment to a different one. In the process of further development and evolution, Orchestration of containers was also a big problem to be handled, so there we got the orchestration tools like Kubernetes, Swarm, etc

I got the opportunity to work with Kubernetes, especially Google Kubernetes Engine (GKE), which is one of the managed Kubernetes services from Google, so I explored and dealt with many containers, be it storage, network, security, etc.
So dealing with security is a challenge that many can relate to. Many buzzing questions come over the technical blogs, forums etc. like, How do I secure my containers? How can I secure service to service communication?
One of the methodologies that DevOps Practitioners do follow is setting up SSL certificates installations.
SSL protects your sensitive information as it travels across the world’s computer networks. SSL would :
- Encrypt our sensitive Info
- Provide Authentication
- Provide Trust
So, how do we add SSL certificates to our Kubernetes Cluster, at what level/type we can add those and how do we secure?
Let’s start by giving a brief intro to our environment, we use micro-service architecture running on GKE and established Loadbalancers on top of that access outside the cluster i.e., from the external world. So I deployed load balancers for that and it worked fine with the Google LoadBalancer service.
Before we go onto Setup guide, let’s understand “Ingress”. Kubernetes Ingress allows external users and client applications to access HTTP services. Ingress has two components:
- Ingress Resource: Set of rules for the inbound traffic to reach Services
- Ingress Controller: This controls the rules which are set by the Ingress Resource
Prerequisites
Make sure that you have the following before set-up on GKE
- Google Cloud Account with necessary privileges
- Running GKE Cluster with your deployments and services
- Ingress Controller: Fortunately Google Kubernetes Engine comes with the GCE Ingress Controller, so we don’t need to install it manually
- SSL certificate: It has two parts: one is a certificate(.cert) and the other is private key (.key)
Procedure to Set-up
1. Deploy the service yaml which you want to expose it to the external world with type as “NodePort”, use the below sample yaml:
apiVersion: v1
kind: Service
metadata:
name: XXX-yy
labels:
app: XXX-yy
environment: prod
spec:
ports:
- protocol: TCP
port: 80
selector:
app: XXX-yy
environment: prod
role: marketing
type: NodePort
2. Next step would be to create SSL secrets in our GKE cluster, Kubernetes provide a secure way through which we can pass our configs to GKE using Secrets.
kubectl create secret tls #NameOfTLSsecret \ --cert $PathToCRTFile.crt --key $PathToKeyFile.key
3. Now let us deploy the Ingress resource yaml which has all the configurations in it like, Ingress rules
apiVersion: extensions/v1beta1
kind: Ingress
metadata:
annotations:
kubernetes.io/ingress.global-static-ip-name: "prod-XXX-ip"
kubernetes.io/ingress.allow-http: "true"
name: prod-XXX-yy-ingress
labels:
app: xxx.ai
environment: prod
namespace: default
spec:
rules:
- host: XXX.yy
http:
paths:
- path: /
backend:
serviceName: XXX-yy
servicePort: 80
- path: /*
backend:
serviceName: XXX-yy
servicePort: 80
tls:
- hosts:
- xxx.yy
secretName: prod-XXX-tls-secret
Add annotation ‘kubernetes.io/ingress.allow-http: “true”‘ and add http to https redirection in Nginx configurations. So whenever we search for http://xxx.yy, it will automatically redirect to https://xxx.yy.
Use the following code snippet
# Replace '_' with your hostname.
server_name _;
if ($http_x_forwarded_proto = "http") {
return 301 https://$host$request_uri;
}
This we have to do manually here in NGINX because GCE Ingress doesn’t support http->https redirection.
Here, take care of Path context, Nginx ingress and GCE ingress work differently. Consider this case- suppose we give path as “/” only, GCE Ingress Controller will successfully make us land onto the main page but everything else like skyl.ai/contact will result in Google Loadbalancer Default backend. So to resolve this problem we add “*”.
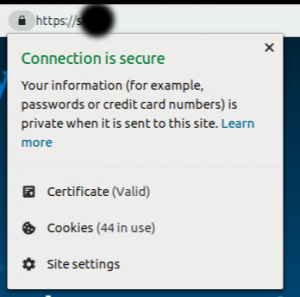
So here we go, you can take a look below, where we save our “connection is secure”.
Conclusion
Thus, installing certificates to our services makes our environment secured. There are many methodologies to secure our platform, adding SSL is one of the finest and recommended DevOps practice.




